How fraud gets staged and paid out, and why investigators need to see the whole sequence without exposing themselves
Fraud frameworks are usually written by people who have never had to stop it.
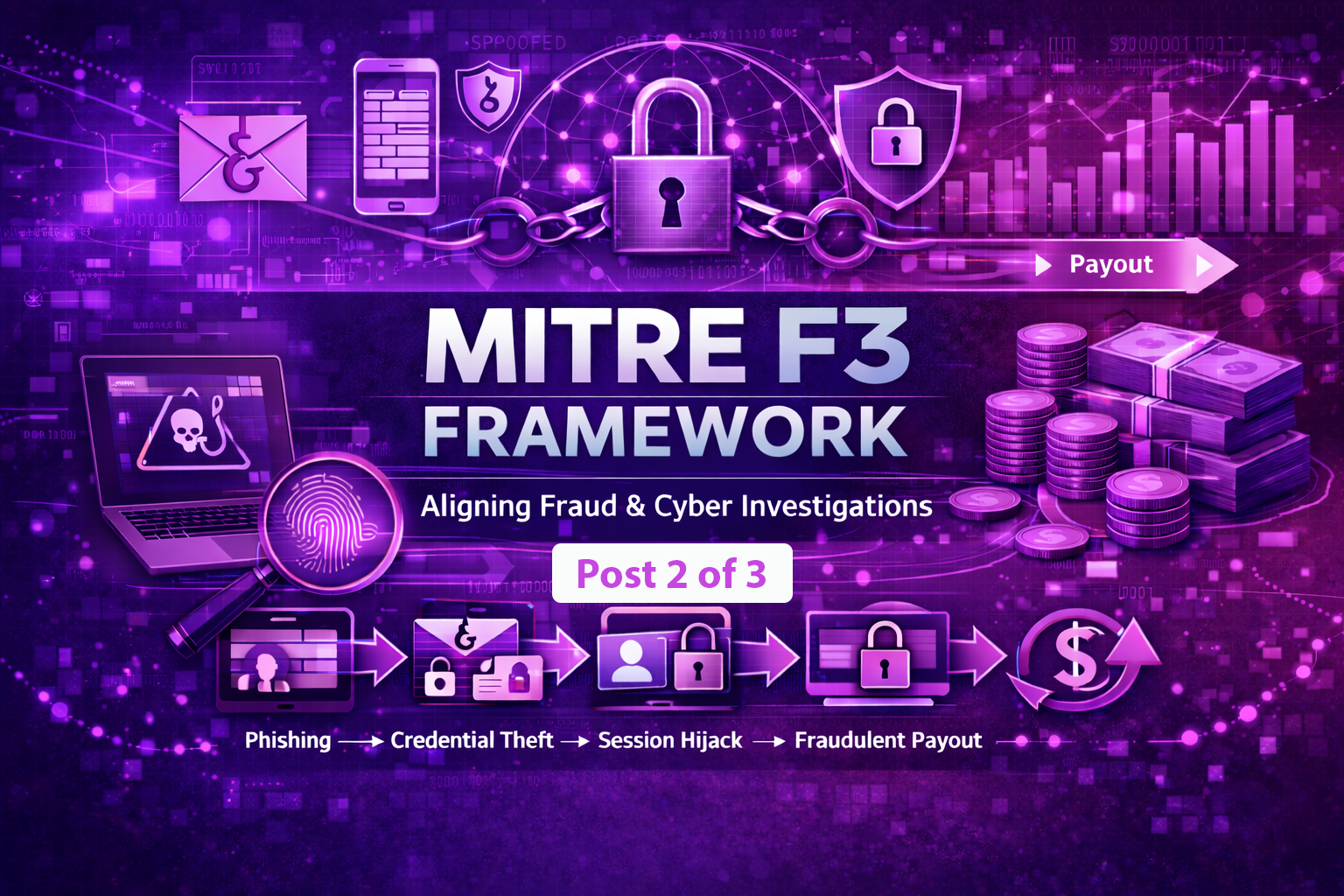
Everyone talks about initial access. Phishing, credential theft, lateral movement. The playbooks are solid. But that’s not where fraud wins. Fraud wins in the middle-ground: when the actor starts preparing the environment, testing controls, moving money, and you’re watching it happen in real time with no safe way to investigate.
That’s what changed in MITRE F3.
The sequence matters more than the moment
MITRE’s new framework adds two tactics that ATT&CK left underspecified: Positioning and Monetization. Translation: what happens after the actor gets in, and what they do to turn access into actual financial loss.
Positioning is the setup phase: Accounts get prepared, data gets staged, controls get tested. A lot of this happens behind the scenes, small actions stacking up into a configuration that’s harder to stop later. You’ll see account modifications, permission changes, reconnaissance of financial systems. It looks like noise until you see the sequence.
Monetization is the finish. That’s where assets move out of your control into theirs. Wire transfers, cryptocurrency movement, account drains. The outcome is visible. The problem is figuring out what led to it. Because by the time you see the loss, the positioning phase was already done.
The real value of F3 isn’t that it renames things. It’s that it forces teams to stop treating access, manipulation, and extraction as separate incidents. They’re one sequence. The work in the overlapping area is where you stop fraud.
The money is already on the move
The FBI reported nearly $21 billion in cyber-enabled crime losses in 2025. MITRE’s data points to $580 billion in fraud and scams globally. That’s not because attackers are better at breaking in. It’s because we’re not paying attention to what they do after they’re inside.
A suspicious login used to sit in one category. An account change in another. A transfer attempt in a third. You’d investigate them separately, compare notes later, and by then the money was already moving.
With F3, the sequence comes into focus. That login, that account change, that transfer attempt… they’re not three separate incidents. They’re three moves in one attack.
The investigator’s dilemma
Once your team sees the sequence clearly, they need to act fast. An investigator needs to validate activity across accounts, systems, and platforms. They need evidence that holds up. They need to move before the next step in the sequence completes.
Cue the shared endpoints, standard access logs, and credential sharing. The tools they use to investigate often add the same risks they’re trying to contain. You’re trying to stop an actor from moving money, but your investigation process is the one creating exposure, contaminating evidence, or tipping off the attacker that they’ve been spotted.
F3 now gives you a concrete sequence. Next week, we’ll dig into how teams can act on it.